If you’ve been following the news recently, you’ve almost likely heard about cybersecurity issues impacting a few of the world’s most important organizations. While cyberattacks may appear to be an issue just for major enterprises — and they are — they affect companies of all sizes & sectors.
Gartner, Inc. estimates that businesses will need to spend more than $170.4 billion every year on cybersecurity defense measures by 2022. Due to an increase in spyware and web-based attacks, specifically ransomware attacks. SonicWall discovered (via PBS) risen % worldwide and 158 % in North America just between 2019 and 2020.
-
Role-Based Access Control Can Help You Protect Your Data (RBAC)
The digitization of business processes and services has saved businesses billions of dollars throughout the world. It enhances corporate efficiency and creates more effective outcomes as more elements are automated and linked to online platforms. However, once any platform is hooked up to the internet. It opens the door for hostile actors to enter and attack.
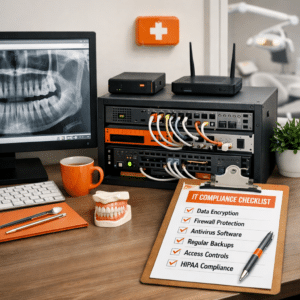
Data breaches need several levels of access. That’s why it’s critical to protect all critical data to prevent a digital file leak. The best method to reduce these risks is to ensure that only necessary staff has access to key files and data. To do this, businesses should employ role-based access control (RBAC) software. It regulates access to specific data and enables only authorized workers to view and access it. Because it prohibits hackers from accessing limited and protected data. RBAC is an excellent technique for dramatically boosting a company’s security.
-
Critical Cybersecurity Solutions: Multifactor Authentication and Virtual Private Networks
Almost all online application attacks use credentials that have been hacked or stolen. Businesses may use two-factor authentication (2FA), multifactor authentication (MFA), and end-to-end encryption to add an extra layer of security. By increasing the number of secure authentication methods available, attackers will have a much harder time breaching this extra layer of security.
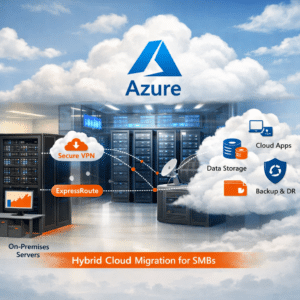
Using an insecure Wi-Fi network also allows hackers to break in and wreak havoc. While most workplace networks are secure, today’s business extends well outside the office, making companies exposed to unsecured networks – a lesson many learned the hard way during the current pandemic. It is vital to invest in a dependable virtual private network to combat this (VPN). Organizations may maintain a mobile workforce while still attempting to secure their cybersecurity by using VPNs to create private tunnels.
-
Consider developing custom software for cybersecurity
While many commercial off-the-shelf (COTS) software solutions are generally supported by firms with solid cybersecurity procedures. Their pervasiveness may make them a more attractive target for hackers. Raising the possibility that they may be the open door that exposes a business. Investing in bespoke software development. Whether it’s brand-new solutions or custom interfaces with existing COTS software, may both restrict and prevent attackers from trying to breach a network.
However, if you decide to go this route, you must evaluate custom software developers. They make sure that those who have not only the advanced skills to build and/or implement a solution. But also the information security expertise and industry-specific experience. It ensures that your software suite can fulfill all of the company’s business and security needs.
-
Automated data backup and recovery from a remote location
Internal business systems are especially vulnerable to data loss and server failure. A range of other technological disasters are there if they are hacked.
To avoid this, business owners can prepare ahead of time. They use automatic remote backup and restoration deployment services to ensure data is preserved on a single, reliable source that can be quickly restored in the case of a disaster. This can help limit the impact of ransomware attacks, which can encrypt your data and render it unusable.
-
Instruction and Practice Make it flawless.
Regardless of the effectiveness of your company’s firewall. It should be a crucial investment as well as a must for any cybersecurity measures— or any other security solutions your organization employs. Your workers will be the first and final line of defense when it comes to cybersecurity.
Because almost 90% of cyberattacks are driven by some level of human error, it is critical to teach personnel what to look for when it comes to phishing attempts and other cybersecurity dangers regularly. A well-informed employee can substantially reduce your cybersecurity vulnerability. Whether it’s through frequent communication from your IT pros or third-party training on the latest tactics and what to look out for.