Chances are, you’ve at least heard the term firewall before. A fairly recent term, it was first used as a computing term in the 1983 movie WarGames before it was ever introduced into mainstream computing. Thanks Matthew Broderick! Since then, the term has expanded and grown to include a variety of approaches. Let’s dig into what a firewall does, as far as each of the various types are concerned.
First, What Does a Firewall Do?
Named for the protective measures that are built into the structure of connected homes and multiple-resident buildings, a firewall on your computer serves much of the same purpose as its namesake. Just as the residential firewall helps to keep a fire from spreading, a computer firewall monitors your network traffic to prevent unauthorized connections from being made. As a result, a properly configured firewall is an essential component of a smart business’ cybersecurity strategy.
Let’s explore some of the different types of firewalls out there, and what they do.
Firewall Varieties
Virtual Firewall
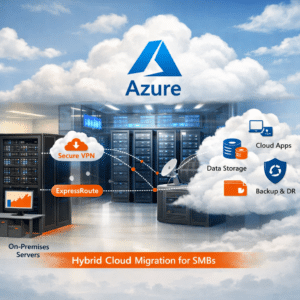
A virtual firewall is one that is hosted in the cloud, meant to protect an environment that is hosted in the cloud or within a virtual machine. As such, it can be customized to the needs that the user has of it, whether they require a specific application to be protected or an entire cloud environment.
Stateful Inspection Firewall
Most modern infrastructures feature this version of a firewall which performs a function known as dynamic packet filtering. Basically, for traffic to pass through the firewall, it needs to be the correct “state.”
Unified Threat Management Firewall
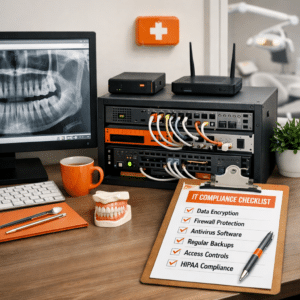
With a UTM firewall, the firewall’s capabilities are augmented by the inclusion of antivirus software. Intentionally easy to use, UTM firewalls can protect a business’ email inbox or defend a remote worker from threats, along with many other necessary safeguards.
Is a Firewall a Requirement for Your Business’ Cybersecurity?
In a word: yes… with the caveat that real cybersecurity will require more than just a firewall to be effective. While a firewall is an important piece of your cybersecurity strategy, it is just that: a piece. Truly effective cybersecurity needs additional safeguards in place.
That’s where we come in. We can help you maintain your business’ IT as a whole, including the protections that defend it. Give us a call at PHONENUMBER to find out what we could do for you.