Sometimes the word “value” is associated with “bad,” like getting the generic brand of certain goods at the department store. However, sometimes you can get some bang for your buck, so you should at least consider some of the value options–particularly for expensive devices like smartphones.
We’ve seen a few social media posts over the last week or so claiming that Android and iPhones have been getting a COVID-19 tracking app installed without getting permission from the user first. People are worried that their privacy is at risk. Here is an example of one of the posts that have been making rounds across Facebook: **VERY IMPORTANT ALERT!***A COVID-19 sensor has been secretly installed into every phone.Apparently, when everyone was having “phone disruption” over the weekend, they were adding COVID-19 Tracker [SIC] to our phones! If you have an Android phone, go under settings, then look for google settings and you will find it installed there. If you are using an iPhone, go under settings, privacy, then health. It is there but not yet functional. The App can notify you if you’ve been near someone who has been reported having COVID-19. There is a little bit of misinformation here. First of all, there really isn’t a way to sneak a “sensor” onto a device through a software update unless there is already some hardware in place that does the sensing. This immediately tells us that something about this is at least a little bogus, because from a technical standpoint, the sensationalist post misses the mark. Here’s what really happened. Google/Apple Didn’t Sneak a COVID-19 Tracking App On Your Phone – They Pushed a Security Setting Google and Apple have been working together to build a framework that app developers can use for apps that notify users if they may have been exposed to COVID-19. They didn’t sneak a COVID-19 app onto your phone without your consent. The two companies added a setting to enable the use of Google and Apple’s COVID-19 Exposure Notification system. This system is the groundwork that official COVID-19 notification apps can use. State and local governments are responsible for developing the apps, but they can use Google and Apple’s secure platform in order to get them to work. If you follow the steps in the article and on Android, go to Settings and then Google Settings, you’ll see that the option to opt-in is disabled. The same with iPhone users; by going under Settings, then Privacy, then Health, you’ll have an option to opt in. Even if you opt in, you still need to install one of the official apps, most of which aren’t even released yet. Again, this is just the groundwork. This Isn’t a COVID-19 Tracking App Just to be perfectly clear, unless you manually installed something, your Android or iPhone isn’t just going to start tracking you and your friends and family to see if you have COVID-19. If you go into your settings as mentioned in the above Facebook post, you’ll see that you either need to install or finish setting up a participating app before the notifications can even be turned on. Apple and Google even confirm this in a joint statement saying “What we’ve built is not an app – rather public agencies will incorporate the API into their own apps that people install.” API stands for Application Programming Interface. Basically, Google and Apple have developed a standardized system to make it easier for states and local governments to build an effective app to notify users if they may have been exposed to COVID-19, but Google and […]
To begin, check the version of Android that you have installed. A few of these tips will require that you’re using Android 10, and some may not work on all devices. Interacting with Your Android Notifications How to Clear Your Notifications Once a notification has, well, notified you of something, its job is done, so it can be dismissed. Doing so is as simple as swiping it to the right or to the left. Dismissing all your notifications at once only requires you to scroll to the bottom of the notification list and select the Clear all option. Silent notifications can be cleared by tapping Close. Some notifications will only dismiss if the process it describes is no longer active. For instance, a notification that informs you that your music player of choice is active will require you to stop the music before the notification will go away. How to Snooze Your Notifications You can also “pause” your notifications by snoozing them. This will require you to activate snoozing in your Settings. Under Apps & notifications, Notifications, and Advanced, you’ll find the option to Allow notification snoozing. Once you’ve done so, you can snooze an individual notification by slightly dragging it to the side and selecting the Snooze option (which is presented as a small clock icon). The Down arrow allows you to select the time that the notification will be postponed. How to Review Your Options Some notifications have multiple options for you to act upon. Expanding these notifications is just a matter of pressing the Down Arrow and making your selection from the options that pop up. Selecting Your Notifications How to Change Your Device’s Notifications In your Settings, select your Apps & notifications and in there, Notifications. You can then select your default notification options from the following options: On lock screen Allow notification dots Default notification sound Swipe fingerprint for notifications Do Not Disturb Activating and Deactivating Notifications for Certain Apps There are multiple options available to you in terms of setting your notifications. In your Settings application: Select Apps & notifications, and from there, Notifications Under Recently sent, you can see all the applications that recently sent you notifications. From there, you can turn off all an app’s notifications, among other capabilities. From the notification itself: Tap and hold your notification, and then tap the gear icon that appears to represent the Settings. You can then select the settings of your choosing, either to Turn off notifications or to select which notifications are Alerting or Silent. In the actual app, you may have the option to change your notifications in the settings as well. Selecting which Notifications Can Interrupt You Some Android devices enable you to select the notifications that an app will provide. Alerting will alert you with a sound, a lock screen message, and a status bar icon. Silent will obviously not provide a sound or vibrate but will still provide a notification if you swipe down on your screen. You have a few options as to how to select these settings. In the Settings application: Tap Apps & notifications, and then Notifications […]
It was discovered that users who set a particular image as their phone wallpaper on Android devices suddenly found their phone crashing. Once the wallpaper is set, the phone will refuse to boot back up, even in safe mode. This means the only way around it is a hard factory reset, which will lose everything on the phone that isn’t backed up elsewhere. Users are able to safely view the image, and even download the image on their device. The issue occurs once the image is set as a background wallpaper on Android devices, especially newer phones, and it seems to affect Samsung phones especially. Let’s Take a Look at the Infamous “Cursed” Android Wallpaper In a Twitter post by user @Universeice, we get a glimpse of the image and the warning not to set it as a wallpaper. Definitely heed our warning and do not attempt to make the image your wallpaper, but it is safe to view: WARNING???Never set this picture as wallpaper, especially for Samsung mobile phone users!It will cause your phone to crash!Don’t try it!If someone sends you this picture, please ignore it. pic.twitter.com/rVbozJdhkL u2014 Ice universe (@UniverseIce) May 31, 2020 Why Does This Image in Particular Break Android Phones? After doing a little research, this photo was taken last year by photographer Guarav Argawal, and ended up on a lot of popular smartphone wallpaper sites recently. Argawal owns the copyright to the image, which means it probably should not have been made available on these wallpaper sites. The issue has to do with hidden data stored within the file itself. There isn’t anything malevolent going on here – any image can have hidden metadata stored within it. Most digital cameras, for example, record the type of camera and settings used, the time and date, and other information automatically when taking a photo. There is a specific type of data called the ICC profile, which has details about the color profiles of an image. All of our modern-day devices have limited colors that they can actually display. Our eyes are pretty limited to what colors we can see, so it doesn’t usually affect us. Color profiles set standardized ranges of colors used in an image that devices can use so colors are relatively uniform across our devices. Ask a graphic designer or photographer and they will have a lot to say about their frustrations with color profiles. That said, the ICC profile used on this image was a fairly uncommon one, and likely not something that Android was configured to use for a Wallpaper. In fact, simply saving the image using a standard color profile makes it safe to use, although it does make the image a little more visually dull. The craziest part about this image, is that if it weren’t for a single pixel, it would likely work just fine. Combined with the uncommon ICC profile, there is a single pixel (a tiny, nearly invisible dot of color) that causes the actual conflict that crashes Android phones. You can’t see it by looking at it, but somewhere in the pinkish lining on one of the clouds is a single pixel that most modern smartphones just can’t handle existing on the wallpaper! Okay, I Won’t Set This Image as a Wallpaper. Am I Out of […]
That’s why we wanted to share how your business could exercise mobility, while still preserving security. Why You Aren’t Safe as a Small/Medium-Sized Business Once upon a time, cybercrime was a simple animal. A target was picked, and the method of breaching it was developed. This meant that the smart strategy for cybercriminals was to focus their efforts on larger targets, as breaching them would be more profitable for cybercriminals to take the time to do. Unfortunately for the SMB, this is no longer the case. Nowadays, like many other industries, cybercrime has largely become automated. So, once an attack is designed, there is no reason that a cybercriminal wouldn’t use it against a wide variety of businesses. It’s a little like using a bug zapper compared to the traditional flyswatter–you actually have to actively swing around the flyswatter, whereas a bug zapper allows you to set it up and let it do the work for you. Less effort, for equal (or really, improved) results. Furthermore, a mobile device does tend to invite a greater risk of other kinds of cybercrime. Actual device theft is much easier when the device in question can be casually picked up and walked off with by a stranger, which is more likely to happen outside the office than within its walls. Convenience is a cybercriminal’s best friend. What to Do About It Therefore, you need to make sure that the mobile devices your employees are using throughout their day have the proper protections, and that (perhaps even more importantly) your employees are actually using them, and properly. Here, we’ve put together a quick guide to help you get started with a more secure mobile strategy–and to hopefully make it more memorable, it follows the alphabet! Mobile Security, as Simple as A-B-C-D-E Authentication Okay, so one of the foundational concerns of the mobile security issue is that it is harder to ensure that only someone with permission to access data is actually going to be accessing it. Let’s face it, all it takes to potentially have a device stolen is for someone to leave their phone unattended in the coffee shop as they add more creamer. However, with the right authentication measures, the risk of the thief accessing data is greatly reduced. Enforcing strong passwords and requiring two-factor authentication measures for your data helps to restrict access to your data to just the people who should have it. Therefore, this is the first step to any data protection process. Backups As we will get into, a big part of keeping the data accessible on mobile devices safe is the capability to delete it. As a result, it is important that you can then restore this data and continue using it once the issue has been resolved. Maintaining an up-to-date backup will ensure that you are able to do so. Keep checking back on this blog to learn what makes a backup as reliable as can be, or give us a call to find out. Control While yes, the mobile devices that your employees own are their property, you cannot allow them to use them as a part of a mobile device strategy if they are going to expose your business to security threats or vulnerabilities. The apps a user installs can contribute to both, so […]
Keep Your Phone with You in Public This one is a bit of a no-brainer, unless you want to have your phone stolen. You should never leave your phone unattended in a public place. Not only could your own data be put at risk, but if you’ve accessed company documents via a Bring Your Own Device policy, who knows what the person who took your device might find before your device is remotely wiped? Besides, phones are by no means cheap, so it isn’t something you want to lose anyway. Keep Your Credentials Safe Most phones today offer to store things like passwords, PINs, and payment card details in order to make things more convenient for the user. However, this holds true if the user isn’t actually you, but is a cybercriminal who has stolen the device. It is better to simply not store these kinds of credentials in your phone, but if you absolutely must, only use a secure application to do so. If you aren’t sure which ones are secure, we can steer you in the right direction. Use Networks Wisely While Bluetooth and Wi-Fi are extremely useful means of connecting to the Internet and the peripherals you are trying to leverage, doing so without being mindful of your security is a dangerous prospect. Unprotected and unsecured networks can open your device to threats (along with any data stored on it). Do your best to avoid connecting to unknown networks and signals to keep from leaving your phone vulnerable to threats. Regularly Remove Data from Your Phone Your phone has a pretty good memory (so to speak) which means that it will retain a lot of data. Whether it’s your autocomplete feature keeping a record of personal data you have typed, or your browsing history providing an in-depth summary of your use of your phone, hackers and cybercriminals find precisely this kind of information to be valuable to them. Clearing this data reduces the information that a hacker could potentially access. When it comes to protecting your data – both business and personal – you need to consider all the ways that it is vulnerable to hackers. SRS Networks can help you do so. To learn more, reach out to us at (831) 758-3636.
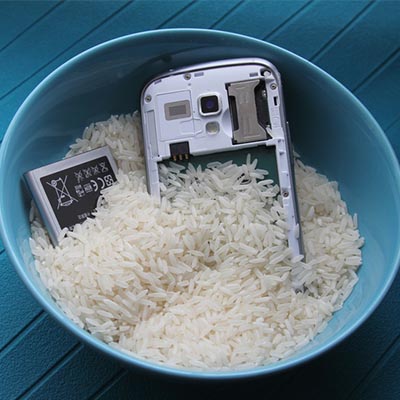
One thing to keep in mind is that many manufacturers are making devices that are, at the very least, water resistant. These devices are given an International Protection (IP) score, which is based on the International Electrotechnical Commission (IEC). This rating is given to any consumer device, and it designates how much protection a consumer can expect from it. For example, a device classified as IP67 is resistant to dust and can be submerged in water no more than one meter deep for up to half an hour. The only difference between this and an IP68 device is that the IP68 guarantees protection in 1.5 meters of water for up to half an hour. Of course, you didn’t come here to learn about the semantics related to device protection classification–you want to know what to do if your device falls in water. Here are some decent catch-all steps you can take to potentially save your device. Turn Off Your Device: Be sure to turn off your device as soon as possible. Don’t try to plug it in or shake it. Don’t blow in it or use a blow dryer to try to save it. Just follow the steps below and don’t stray from them. Remove your SIM card and any other expandable storage. Remove the battery if possible: Some phones don’t have the removable battery, so if it doesn’t, don’t just pry it open. Have a professional do it for you. You can always check out YouTube for tutorials as well. Use an absorbent rag to dab your phone dry: Try not to wipe it around, as this could spread the liquid too much. Place the phone in a plastic bag filled with uncooked rice: The rice will absorb the liquid. Let your phone dry for a day or two before trying to turn it on. Turn it on: If this doesn’t work, try charging it. If the device doesn’t charge, the battery could be damaged. You will want to work with a professional to do this, if you haven’t already done so. If it seems to work right, make sure everything does: Make sure you test the screen for responsiveness, as well as the speakers and microphone. By following these eight steps, you’ll maximize your chances of getting away from a phone-meets-liquid incident unscathed. If you found this blog helpful, be sure to share it with anyone else who might benefit from it.