The first thing that we should mention in this article is that Windows 7 will be losing support this upcoming January, and with so many people/businesses still using machines running the decade-old operating system, Microsoft knew they needed to make Windows 10 that much more accessible. Their strategy is to provide Windows 10 as a cloud service. In launching Microsoft 365, the software developer has made it easier to upgrade away from Windows 7 and 8.1. For the modern business that depends on their Windows 7 workstations, this provides them with an option to get their business moved over to a platform that’s security is strong and up-to-date. Windows 10 has been remarkably resilient as threats continue to multiply. In fact, there are some people in the industry that argue that Windows 10’s Windows Defender is one of the best antivirus solutions ever made for a personal computer. It may be that for an individual user Windows 10’s built-in security is enough to protect them against a web filled with viruses and malware. For the enterprise, however, it is vigilant to have added security in the form of a dedicated antivirus and powerful spam blocker. That’s not to deride the improvements Microsoft has made to its internal security system, it just provides more control for administrators whose job is keeping these threats from damaging an organization’s operational effectiveness. What to Expect from Windows 10 Enterprise Security As stated above, Windows Defender is a strong antivirus, but the real benefit to Windows 10’s security solutions is the improvement in identity and access management and data protection. In improving Windows 10’s identity and access management systems, Microsoft has made a point to improve security around the access points. They’ve thoroughly overhauled the way they authorize users, groups, and other systems to access data on Windows 10-controlled networks or devices. With this enhancement, administrators have more options to outline the ownership of objects, user rights, and data that is available for reporting. User Account Control (UAC), found in the most recent version of Windows, is enhanced in Windows 10. It works to prevent malware by blocking the installation of unauthorized applications and prevent non-administrators from changing system settings. Another change is the use of two-factor authentication to gain access. By setting up a two-factor authentication system, users will be forced to have access to additional accounts to gain access, mitigating access problems that come from stolen passwords. Additionally, Windows 10’s security includes BitLocker, a data protection feature that integrates with the OS and is used to address the near-constant threat of data theft (or unauthorized exposure). There are also dynamic features such as the Trusted Platform Module, which provides hardware-based security functions, and the ability to secure the Windows 10 boot process. Every security feature should be added into a dedicated Windows Information Protection policy that can be set per device or over an entire network. Windows 10 is one of the strongest operating systems ever created in dealing with threats. Learn more by contacting our IT experts today at (831) 758-3636.
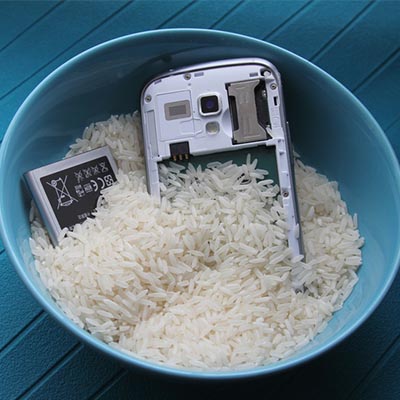
One thing to keep in mind is that many manufacturers are making devices that are, at the very least, water resistant. These devices are given an International Protection (IP) score, which is based on the International Electrotechnical Commission (IEC). This rating is given to any consumer device, and it designates how much protection a consumer can expect from it. For example, a device classified as IP67 is resistant to dust and can be submerged in water no more than one meter deep for up to half an hour. The only difference between this and an IP68 device is that the IP68 guarantees protection in 1.5 meters of water for up to half an hour. Of course, you didn’t come here to learn about the semantics related to device protection classification–you want to know what to do if your device falls in water. Here are some decent catch-all steps you can take to potentially save your device. Turn Off Your Device: Be sure to turn off your device as soon as possible. Don’t try to plug it in or shake it. Don’t blow in it or use a blow dryer to try to save it. Just follow the steps below and don’t stray from them. Remove your SIM card and any other expandable storage. Remove the battery if possible: Some phones don’t have the removable battery, so if it doesn’t, don’t just pry it open. Have a professional do it for you. You can always check out YouTube for tutorials as well. Use an absorbent rag to dab your phone dry: Try not to wipe it around, as this could spread the liquid too much. Place the phone in a plastic bag filled with uncooked rice: The rice will absorb the liquid. Let your phone dry for a day or two before trying to turn it on. Turn it on: If this doesn’t work, try charging it. If the device doesn’t charge, the battery could be damaged. You will want to work with a professional to do this, if you haven’t already done so. If it seems to work right, make sure everything does: Make sure you test the screen for responsiveness, as well as the speakers and microphone. By following these eight steps, you’ll maximize your chances of getting away from a phone-meets-liquid incident unscathed. If you found this blog helpful, be sure to share it with anyone else who might benefit from it.
The Criteria Ask yourself the following questions about your messaging application: Are my messages encrypted (and how encrypted are they)? How transparent is the application to scrutiny? How are messages deleted? How much metadata is kept? We’ll go through each question to help you ascertain if the messaging platform you use is secure enough to use for business. Are My Messages Encrypted? (And How Encrypted Are They?) Encryption can scramble data so that it is difficult to read to all those who don’t have a decryption key. We don’t want to get into too much detail, but suffice to say that encryption can make your data much more secure than it would be otherwise. While most major messaging applications use encryption, not all of them follow the most secure of practices. For example, solutions like Google Hangouts and Skype encrypt the messages that users send, but they also retain a copy of the encryption keys. This is so they can access the messages sent to collect data for advertising purposes. Unfortunately, this also means that the data will be vulnerable if a cybercriminal manages to make their way onto the application’s servers, or if the government were to issue a search warrant for them. Thankfully, end-to-end encryption is more common with these kinds of apps, where the application holds the keys that encrypt the data. The users also have a key to decrypt the data, meaning that no other external party can access the contents of the messages. Some of these include WhatsApp and Signal. While Skype does offer this option, it isn’t enabled by default. How Transparent is the Application to Scrutiny? It’s important that your messaging application provider not only is honest about the state of security, but is also evaluated by an independent and impartial expert that comes to the same conclusion. This means that open-source applications are usually more trustworthy, as they have been the subject of much closer scrutiny over the years. Examples of these applications include Signal, Telegram, and Wickr, while WhatsApp and Facebook Messenger aren’t true open-source, but are based on the same protocol as Signal. An application that is closed-source, like iMessage, trusts the developer entirely to maintain the security of the messages sent. How Are Messages Deleted? What happens to messages after they have reached their destination and been deleted? In truth, deletion might be the best way to ensure the privacy of important information. Applications that automatically delete messages within a certain amount of time can be great for security. For example, Skype, Telegram, and Signal all have this capability. WhatsApp even goes as far as deleting messages within 13 hours. Not all apps feature self-deleting messages, and to be fair, nobody is stopping the recipient from taking screenshots of messages, either. Thus, security is left to the discretion of the recipient. How Much Metadata is Kept? It’s also critical that your chosen application is protected by the metadata it stores. Metadata contributes to security through user profiling, which stores data of both the sender, receiver, time of communication, IP address, and the device used. Thus, knowing what kind of data is stored by the messaging application will help you best preserve the security of this data. SRS Networks can help you implement secure methods of communication for your business. […]
Misconception 1: Our vocabulary is limited to “Did you turn it off and on again?” Yes, yes, ha ha. This one has become the go-to punchline for almost any joke having to do with IT. However, consider what humorist Leo Rosten said: “Humor is the affectionate communication of insight.” In other words, jokes tend to poke fun at a larger truth – in this case, IT resources have gained the reputation of asking this question so often because they do ask it quite often. This is because it actually is an effective way to resolve many issues. Reboots have proven their value countless times over, so when we ask you if you’ve already tried doing that, we’re actually taking a lot of explanations for your issue out of consideration. This allows us to more efficiently troubleshoot the actual problem – and if you hadn’t yet tried a simple restart, it might do the trick. Misconception 2: IT is actually, like, super easy to manage. With computers being remarkably more user-friendly than they once were, it also isn’t all that uncommon for many users to assume that everything that IT does, they could probably do for themselves. Technically, in a lot of cases, yes… but it would probably be a mistake. In IT, while a process might be simple in and of itself, there’s a good chance that there are a lot of other considerations to take into account. For instance, let’s look at the process of setting up a new workstation. It’s a pretty plug-in-and-play process, right? Right – except that there’s data transfer, continuity, and security to also consider. On top of that, there’s also the process of getting the new PC ready for use. If done incorrectly, there are a vast amount of ways that your business can be left vulnerable. This is why it is so crucial to entrust these processes to someone who is very familiar with them. Misconception 3: An IT resource is really just a professional Googler. It isn’t uncommon to see an IT professional consulting Google, and sure, it might be unsettling for an end user to see it happening. However, it might help to put things into perspective. IT is one of the fastest-evolving fields in the world, so even the most credentialed and qualified tech might not be completely up-to-date. Therefore, to prevent their actions from causing a bigger problem, a good IT resource will turn to other resources to confirm that they are taking the right course of action. In fact, this makes it actually preferable to bring in a Google-happy tech. It just shows you that the tech is committed to doing their job correctly. At SRS Networks, we’re proud that our technicians know their stuff as well as they do – and know their limits enough to seek out the right answers to your issue. So, next time you experience a problem with your technology solutions, turn your system off and on again, and (if that doesn’t work) give us a call at (831) 758-3636.
Email Subjects Benefit the Reader A key aspect of the fine art of email subjects is that it is there to help the reader determine how valuable the message is. This helps them determine whether it’s worth investing time in. While it might seem easy to see a generic subject line and avoid it, it’s even more tempting to bypass one with no subject at all. This is extremely important for messages that go out to a lot of people. Subject Lines Shouldn’t Be the Entire Message While the subject line is important, it shouldn’t be the entire message. The subject line is only meant to be a glimpse of what the message is about. Save the entirety of the message for the actual message subject body. If the message is complicated enough that you need to explain it so thoroughly in the subject line, then perhaps it’s best to have the conversation in person. The best subjects are short enough to be consumed while providing an adequate summary of what the message is about, keeping the majority of the details for the message itself. Make Sure You Use a Subject If someone doesn’t include a subject on their message, you can assume one thing: the sender doesn’t find it important enough to assign a subject. This basically means that anyone who has a considerable amount of responsibility might never get around to reading emails without a subject, or at best be pushed to the side rather than thrown to the top of a priority list. Did you find this tip helpful? Sound off in the comments below for other topics you might want us to include in future tip of the week blogs.
Chrome OS If you were to really think about it, what application do you use most on your PC? Regardless of what you do with your machine, there is a very good chance that the answer would be your web browser. Google, understanding computing trends better than many other companies, decided to make a device operating system that functions a lot like their extraordinarily popular web browser. From the user’s angle, Chrome OS is essentially a suped-up web browser, meaning that many of the applications that come equipped on the device are web-based, and therefore not accessible without an Internet connection. That’s not to say that Chrome OS doesn’t feature plenty of software that can be accessed offline, but to get the most out of the OS, like you would Windows, macOS, or any other OS you would use, you will want to be online. ChromeOS’ primary delivery method is through the Chromebook, Google’s mobile hardware option. There are several different versions of the Chromebook from several of the top hardware manufacturers including HP, Samsung, Acer, ASUS, and Dell. A few manufacturers also offer what is called a Chromebox, which, as you may guess, is a PC that runs Chrome OS. There is also the Chromebase, which is a combination system that provides a display and chrome OS in one. There is also the Chromebit, which is a HDMI-connected dongle that can be used to deliver Chrome OS onto televisions and other monitors. The major benefit of these devices is that they offer an exceptionally easy-to-use interface with secure and fast Internet browsing. Application Integration One neat feature that many Chrome OS-run devices have is that they provide access to multiple sources of software. The Chrome Web Store is the browser-based store has many different options for software. Not only does it carry Chrome themes, it also has stand-alone software extensions that have been developed to help people solve all types of computing problems inside of their Chrome browser. Additionally, many of the Chromebooks come with touchscreens. Many of these devices also have access to Google Play Store apps that are typically used on Android devices, while also supporting Linux-based software. This presents the Chromebook user with a substantial cache of applications in which to choose from. Is Chrome OS Right for Your Business? When trying to establish if Chrome OS is a good fit for your organization, you have to ask yourself three major questions. Does your staff utilize cloud-based software like Google’s G Suite for productivity? Do the local programs you use have cloud-based options? Is the cost reduction worth the limited enterprise software options? If you answer yes to all three, Chrome OS-based computing may just be a huge benefit for your company. If your business is interested in being presented cost effective options for its computing, call the knowledgeable consultants at SRS Networks today at (831) 758-3636.
The late American author Kurt Vonnegut once wrote, “New knowledge is the most valuable commodity on earth. The more truth we have to work with, the richer we become.” Written in the 20th century, it has been put in practice by 21st century businesses. As the Internet has grown, the amount of companies expanded, and the amount of data that those companies collect has grown exponentially, especially now that there is a market for such data.
The password isn’t nearly as secure as it used to be. Hackers have begun to take advantage of extremely powerful solutions designed to brute force their way into accounts by using software to rapidly guessing thousands of passwords per second, making it extraordinarily difficult to prepare yourself for them. What’s the best way to guarantee that passwords aren’t going to be the downfall of your company? A great start is by taking a close look at password best practices and two-factor authentication.
Data security isn’t a matter to be taken lightly, as too many businesses have found out the hard way. Unfortunately, there are far too many simple ways to correct common security issues – enough that it’s foolish not to do so. We’ll review a few ways to fix security issues, after discussing one of, if not the, most egregious security failings in modern history.
Despite what detractors say, regulations are in place for good reason. They typically protect individuals from organizational malfeasance. Many of these regulations are actual laws passed by a governing body and cover the entire spectrum of the issue, not just the data involved. The ones that have data protection regulations written into them mostly deal with the handling and protection of sensitive information. For organizations that work in industries covered by these regulations there are very visible costs that go into compliance. Today, we look at the costs incurred by these organizations as a result of these regulations, and how to ascertain how they affect your business.