Use Proper Password Management
As one of the most important parts of protecting your infrastructure, password management can’t be ignored. Your passwords should be complex, using both upper and lower-case letters, numbers, and symbols. While this might make them difficult to remember, an enterprise-level password manager can make this task easier.
Check for Security Certificates
Before you enter sensitive credentials into any website, you should first check to see that it’s secured with a security certificate. In Google Chrome, you can check this by looking for the green padlock icon next to the URL in the address bar. In general, if you see a website with an https:// in the URL, it’s probably secure, but it’s still best to check the certificate.
Implement a Spam Filter
Hackers tend to use email as a scamming option. They will include links that lead to malicious downloads or fake websites that are designed to harvest your credentials. You can dodge many of these bullets by hovering over the link and checking to see where it goes, before you actually download the file or go to the website.
Be Careful of What You Download
Online “freeware,” will often come bundled with unwanted programs, like adware or browser add-ons. Many of these add-ons can be malicious in nature, so it’s best to always pay attention to end-user license agreement prompts, and to be on the lookout for what you are agreeing to. In other words, don’t leave checkboxes checked unless you actually want what they’re offering.
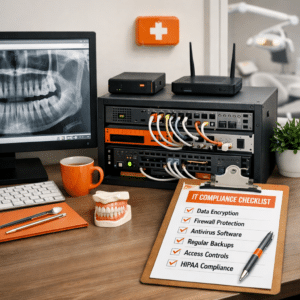
Always Keep a Firewall and Antivirus Solution Active
It’s of the utmost importance to always keep a firewall and antivirus running on your network and its endpoints. Firewalls can keep threats out of an infrastructure, while an antivirus can eliminate the threats that manage to make it through your defenses. Never disable your firewall for any reason.
Use Content Filtering
Most business owners associate content filtering with blocking social media and other time-wasting online content, but its use extends far beyond that. With content filtering, you can keep your users from accessing fake websites or those that contain malware that could negatively affect your infrastructure.
Identify Phishing Attacks
While a spam filter can keep some phishing emails at bay, others will undoubtedly still make it through the restrictions. Phishing attacks use deception to trick users into handing over important credentials or sensitive data. The hacker might even pretend to be someone else in order to extort information from you. Look for spelling errors or inconsistencies if you receive messages from unsolicited sources, and never let your guard down. You can even cross-check the email addresses or phone numbers that you have on file to check if the user is legit or trying to scam you.
Just Use Common Sense
People tend to act impulsively or irrationally when faced with threats like malware and viruses. Instead, you should devote your time and energy into resolving the problem, rather than panicking. Doing so can help minimize the damage done and avoid the threats altogether.
For more great security tips and tricks, reach out to COMPANYNAME at PHONENUMBER, and subscribe to our blog.